
The rate of cyberattacks is alarming. The number keeps increasing every year. According to the FBI’s 2019 Internet Crime Report, in 2018, cybercrime leads to a $2.7 billion loss. This means that you have to up your game when it comes to protecting your website content. You can prevent cyber attacks by controlling any form of data that comes from users.
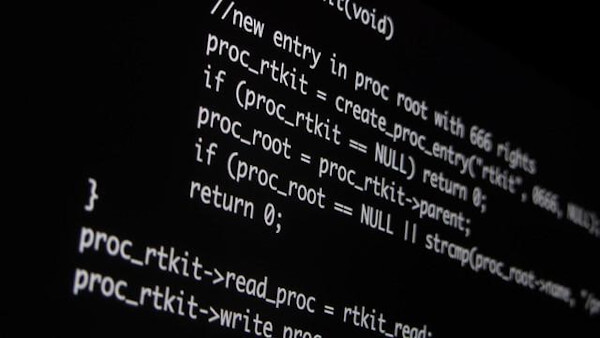
Most website browsers use an anything-goes policy when it comes to security. This is by default. You can change it and implement your very own content security policy (CSP). This is a safer alternative as it gives you full control enabling you to prevent any security issues. It permits you to get rid of any security issues that can occur due to Cross-Site Scripting (XSS).
Using a CSP gives you control over both inline and external scripts which can jeopardize your website’s security. If any issues arise, they will be blocked by a content security policy. CSP can be implemented by a web developer. A content security policy example includes using an HTTP header.
Find a supporting browser
Your first step is to figure out whether your browser supports it or not. For example, CPS 1.0 is supported by the majority of browsers. The CSP supports mobile devices as well. Internet Explorer only supports X-Content-Security-Policy header (CPS header) and sandbox directive. The only browser that supports new directives is Chrome.
Introduce your CSP
Carefully plan out a strategy before getting started with your CSP. If your company has a large website, you might consider transferring inline JavaScript to external files. This gives you control over inline scripts and styles.
Select a strategy
There are two options for a default directive. A blacklist strategy is a method in which everyone is given access to a website except a few sources that might be a threat. A whitelist strategy, on the other hand, is meant to keep the public out, giving access to only a select number of individuals.
A blacklist strategy lets in everyone by default. It is better to start with a default strategy until you are well aware of every source. When you figure this out, switch to a whitelist strategy. This means you will be disallowing everything and only allowing sources that you know.
Work on the configuration
A SecureHeaders sends directives that are supported by your user agent. This configuration helps you to add and change directives based on the action being performed. To change payment controllers just add another script. An advantage of adding another script is that you won't have to send it to your entire site. This configuration means:
- Allowing everything by default,
- Allowing scripts of the same origin,
- Sending CSP reports.
Incorporate violation reports
There are various ways in which a policy violation can be shown. One option is for the policy to be displayed on the browser's console. Use a report only header instead of a content security policy. However, doing so means that only policy violations will be reported. Other content won't be blocked. A violation report and content security policy header show where reports should be sent.
Remove unsafe styles
Some libraries on your website can pose a severe security threat. If you don't utilize certain libraries such as jQuery, then they can be removed. It is essential to remove unsafe files because they may contain JavaScript. Modern browsers can cancel risky styles and scripts, so they are safe.

Check the CDN scripts
Some libraries such as jQuery are usually delivered by a CDN. You can save some bytes by leaving out the Https://. This version has higher chances of being intercepted. It would be great if you could have a code to load a library from your server.
Change scripts
For a simple application, change your inline scripts by adding javascript_include_tag controller_ name to the layout. Larger applications require you to be organized to convert your inline scripts. You can also do this by using Turbolinks. These allow you to individually add a scope to each page and add more scripts per controller. This option may not be suitable for websites that use a lot of page-specific codes.
Convert your JavaScript
Some scripts may require dynamic input. You should separate scripts and data, especially if you don't have a Rail. You can achieve this by making use of static scripts. These make use of data attributes with relevant elements required. You can do this by making use of static scripts. Static scripts always refer to the attributes of elements that matter the most.
Allow AJAX
Use a policy that has a connect-src 'self’ directive. This will allow AJAX to work well with the most applications. Your CSP will convert JavaScript which you will use for AJAX. Use eval to evaluate AJAX responses that use scripts. Add script-scr to be able to use CSP for this functionality. An 'unsafe-eval’ also allows you to separate data from markup. Although this might take more time and effort, it will be worth it once you separate JavaScript.
Conclusion
Making use of a CSP is one of the best ways of maximizing security on your website. You will need to develop a strategy that will be effective when implementing your CSP. This will make it easier for stricter control when it comes to scripts that you allow on your applications. The same applies to styles used for applications.
It would be a great advantage if you could use a CPS that is supported by various browsers. Chrome will support any available CSP. The ultimate goal of using a CSP is to keep converting scripts so that you will have a secure website.


 Copyright 2000-2026, WebSitePulse. All rights reserved.
Copyright 2000-2026, WebSitePulse. All rights reserved.