Page 57
Tweet Your Status - How to Use WebSitePulse with ifttt.com and Twitter
Posted on June 21st, 2012 by Victoria Pal in Monitoring, Tools, TechThere are a lot of interesting ways in which you can use our monitoring services. Engaging in online reputation management is also one of them. A main prerequisite for establishing a good name for you and your business is being transparent. But let's face it, eventually your website will experience downtime. It happens even to the best of sites. And more often than not it is your responsibility keep track of the performance and availability of your website, and take proper action when needed.
 In the unfortunate event of your website going down, for one reason or another, it won’t take long for your visitors to find out. It is better for them to learn about it from you rather than speculate on social networks about the outage. Do you remember how Twitter used to have issues remaining online under heavy use? They came up with what became an internet meme - the fail whale. It was their own way of saying: “Yes, there is a problem and we are working on it”.
In the unfortunate event of your website going down, for one reason or another, it won’t take long for your visitors to find out. It is better for them to learn about it from you rather than speculate on social networks about the outage. Do you remember how Twitter used to have issues remaining online under heavy use? They came up with what became an internet meme - the fail whale. It was their own way of saying: “Yes, there is a problem and we are working on it”.
Exporting Data from WebSitePulse's API to Google Drive
Posted on June 7th, 2012 by Victoria Pal in Monitoring, Tools, Tech, Guides What’s the fun in having a fully functioning API if you can’t play around with it, right? Sometimes data is needed in different forms to serve a specific purpose. APIs are great when the existing interface and available functions are not enough. Getting data straight to spreadsheets is great for custom reports and graphics. So, let’s learn how to do this.
What’s the fun in having a fully functioning API if you can’t play around with it, right? Sometimes data is needed in different forms to serve a specific purpose. APIs are great when the existing interface and available functions are not enough. Getting data straight to spreadsheets is great for custom reports and graphics. So, let’s learn how to do this.
Today we are going to focus on XML and export data with the HTTP API. Before we start, let me remind you that if you want to replicate and build upon any of what I’m writing below, you will need to register for any of our services – paid, trial or free. They will all give you access to our API and what you have in your account.
The Great Firewall of China - Piercing the Golden Shield
Posted on May 31st, 2012 by Victoria Pal in Tech Since we have already discussed the history of the Golden Shield project and how the Great Firewall of China works, it is time to see how the Chinese netizens can get around it. There are a number of ways to get through. Even those without skills can seek help from tech-savvy individuals and still get around the Great Firewall.
Since we have already discussed the history of the Golden Shield project and how the Great Firewall of China works, it is time to see how the Chinese netizens can get around it. There are a number of ways to get through. Even those without skills can seek help from tech-savvy individuals and still get around the Great Firewall.
The different methods to bypass the Great Wall require different levels of dedication and resources. The Chinese government is always trying new techniques to prevent users from circumventing the shield. Controversially, internet censorship is helping smaller industries to develop. Let’s have a look at what’s currently available at hand.
Getting Affiliated With WebSitePulse - One More Way To Benefit From Remote Monitoring
Posted on May 28th, 2012 by Lily Grozeva in WebSitePulse News
Let’s start this week with something different! Today, we are glad to present to you the WebSitePulse affiliate program. Like most good services on the internet, we would like to give our trusted followers a way to further benefit from our services. Now you can earn a pretty penny every month.
Alternatives for Free Cloud Storage in China
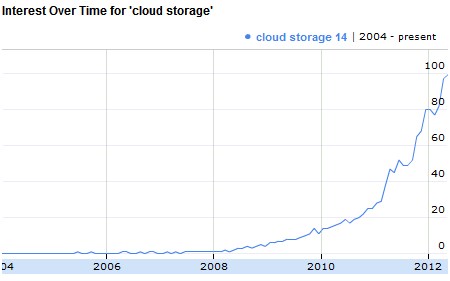
Posted on May 14th, 2012 by Lily Grozeva in TechChina has a long-running practice of censoring and restricting access to foreign services, and cloud storage is no exception. Google Drive is the last service to hit the Golden Shield. It is hard to believe that Google will find solace in the fact that most of the popular cloud storage services are also restricted in China. Five hundred million active internet users are off-limits, while cloud storage is on the rise. There are already quite a lot of great service providers out there. The number of services suggests that there is rising demand. Cloud storage for the masses is still a new and exciting thing.

 Copyright 2000-2026, WebSitePulse. All rights reserved.
Copyright 2000-2026, WebSitePulse. All rights reserved.