Page 55
Why Is My Website Slow?
Posted on February 21st, 2013 by Boyana Peeva in Tech Website speed is important! Having a website that loads and responds quickly for visitors is a good thing as a slow, unresponsive website can frustrate visitors, causing them to leave the page before it even loads, and avoid visiting in the future.
Website speed is important! Having a website that loads and responds quickly for visitors is a good thing as a slow, unresponsive website can frustrate visitors, causing them to leave the page before it even loads, and avoid visiting in the future.
Also, it's important to keep in mind that not everyone has very fast Internet speed. While you can't affect the speed of individual visitors' Internet services, it is important to optimize your website speed and web pages as much as possible, without sacrificing the quality of the website, of course. Another factor to keep in mind is that a fast-loading website may also do better in Google search engine rankings, which can influence your website's traffic.
The first step in increasing the speed of your website may be to check how fast it is currently. You can do so using the free WebsitePulse tools to get an accurate measurement of its current speed and an idea of how much you want to improve. Ideally, your website should load in no more than three seconds.
5 Reasons It's Important to Have an Efficient Web Hosting
Posted on December 17th, 2012 by Kamran Sharief in Whether you’re considering an online business or you’re considering a website that will be an appendage to your already existing business, it’s not only important to have a website that is professionally designed and easy to navigate, but it’s important to have a quality hosting plan in place so that people can visit your website online. While there are plenty of options for hosting, not all webs hosting services are created equal and you’ll need to look for hosting company that offers your business website the features it needs at a price that is acceptable as well.
Whether you’re considering an online business or you’re considering a website that will be an appendage to your already existing business, it’s not only important to have a website that is professionally designed and easy to navigate, but it’s important to have a quality hosting plan in place so that people can visit your website online. While there are plenty of options for hosting, not all webs hosting services are created equal and you’ll need to look for hosting company that offers your business website the features it needs at a price that is acceptable as well.
Increased Demand Increased Services
If the website is a brand-new venture, chances are good that the website is not likely to get a great deal of traffic. In these instances, a less expensive hosting plan such as a shared server hosting option might be the best route to go. These hosting plans are inexpensive and offer your website plenty of features to start with. As your website traffic increases, you’ll need to make sure to choose a web hosting company that can offer you increased services as your website demands them.
How to measure website response time?
Posted on November 28th, 2012 by Lily Grozeva in Tools, Tech Everyone who operates an online business understands the importance of having fast website response times. When webpages are simple to perceive, the user will spend more time on your pages, and are much more likely to spend money while they are there.
Everyone who operates an online business understands the importance of having fast website response times. When webpages are simple to perceive, the user will spend more time on your pages, and are much more likely to spend money while they are there.
The "end user", or the client, or buyer who visits your website, is the entire reason your website was built, and having a deep understanding of how to influence their behavior while on your website can be critical to your business's success.
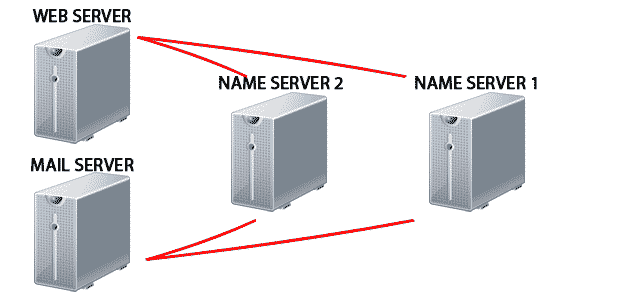
How to check a name server?
Posted on November 26th, 2012 by Lily Grozeva in Tools, TechFor your website to be visible on the internet, your domain name has to be pointed to the name servers of your hosting provider. Visitors are able to access your website using your domain name rather than the IP addresses because of the Domain Name System (DNS).
Bypass the China Firewall Methods
Posted on November 16th, 2012 by Victoria Pal in TechWith their assortment of techniques to prohibit access to websites they do not like, China is probably the country where the “Site not found” errors are most common, with the possible exception of North Korea. This can be frustrating, especially if your website isn’t intended to be politically subversive in any way, but it happens to contain out-of-context keywords that the Chinese authorities have deemed undesirable. This broad brushstroke is unfortunate, but luckily, there are ways to bypass the China Firewall and get past China’s so-called Golden Shield.


 Copyright 2000-2026, WebSitePulse. All rights reserved.
Copyright 2000-2026, WebSitePulse. All rights reserved.