
In today's digital era, cloud computing has become the backbone of numerous businesses. Cloud systems have become the go-to choice for many organizational needs thanks to advantages like unparalleled scalability, accessibility, and cost-effectiveness.
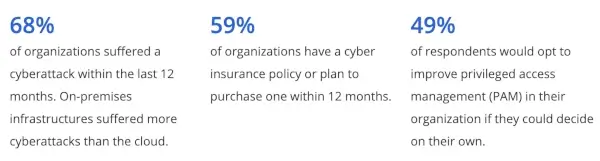
Still, the rapid surge in cloud adoption has attracted the attention of cybercriminals. According to a report from Netwrix, 68% of organizations experienced at least one cyber attack incident in the past year.
With the rising prevalence of cyber threats, businesses must implement robust protective measures to safeguard vital cloud systems. Here, we'll examine critical strategies and best cybersecurity practices to protect cloud systems from cyber-attacks and criminal activities.
Who Provides Cloud System Security?
Most companies choose solutions from enterprise cloud service providers instead of hosting internal servers. Naturally, they expect cloud service providers to handle system security as well. Mainstream players such as Google, Amazon, and Microsoft all offer top protection for their systems.
However, cloud service providers can only handle part of any cloud system's cybersecurity needs — the remaining part falls to the client and the system users. The service providers manage the server-side security, ensuring no compromise on their general system.
But it's up to your organization to manage the client-facing side of the cloud system. Cloud providers can't protect your data when cybercriminals have access to your login credentials.
They also can't protect your organization when your data interacts with other systems outside of theirs. That includes when employees download data and transfer them to third-party devices.
How to Protect Vital Cloud Systems
While cloud service providers handle server-side security, you should implement the following protective measures for the client side of your company's cloud systems and computers.
Implement End-to-End Security
Cyber threats and crimes have advanced beyond antivirus and half-baked security processes. You need the right technology stack and skilled employees to protect cloud systems from cyber threats and risks.
Your cloud systems' security measures must incorporate advanced safety elements, including accurate threat intelligence and the right tools for countering hacking attempts — whether they target traditional websites or web apps.
Furthermore, you should think beyond external threats. Establish measures to protect your company's cloud systems from internal threats and cyber attacks. While it's unlikely that employees will attempt to breach systems, it's not entirely impossible.
Implement Continuous Monitoring and Incident Response
Cloud systems house high-value information that should be under strict security around the clock. Like a bank providing 24-hour protection for its premises, your enterprise should invest generously in protecting its cloud systems.
Implementing real-time cloud systems monitoring is indispensable in promptly detecting and mitigating cyber attacks. That means your organization must implement vulnerability monitoring measures to alert the relevant parties whenever it senses breach attempts.
You may implement this with intrusion detection systems (IDS), security information, and event management (SIEM) tools. These systems help to identify suspicious activities and potential security breaches as they happen.
In addition, an efficient incident response plan helps to minimize the impact of cyber attacks. Your organization must establish well-defined procedures to contain and eradicate threats quickly. That helps to reduce downtime and potential data loss.

Conduct Regular Security Audits and Risk Assessments
The future of cloud communications and its continued security lies in pre-emptive measures. Security audits and assessments of your enterprise's cloud systems will help you stay ahead of evolving cyber threats.
This continuous risk assessment helps you identify any potential point of compromise in the infrastructure.
As standard practice, you must conduct a risk assessment each time you move data to the cloud. This proactive practice protects cloud systems from possible data compromise.
- Schedule regular comprehensive inspections for your cloud system to identify weak points that cybercriminals may exploit to gain access. A comprehensive risk assessment should thoroughly evaluate existing systems, security controls, and the potential security impact of new updates.
- Up to 59% of Mimecast's 2023 survey participants say cyber attacks are growing increasingly sophisticated. And your cloud security measures must keep up. Conduct penetration testing to simulate cyber attacks periodically, exposing areas that require reinforcement. This precaution can identify potential vulnerabilities in your cloud systems and prepare countermeasures for exploitative attempts.
- Security assessments should also extend to third-party cloud service providers. You should also carefully evaluate your organization's cloud vendors' security protocols and certifications. Do that to ensure they comply with 2023 industry standards and regulations.
Strengthen Access Controls
Controlling "who" has access to "what" tops the current cloud security trends list.
While aspects of your cloud system may be available to your end clients, your security measures should limit access to cloud system operations related to internal processes.
Total cloud system protection from cyber attacks is enhanced when you control access to sensitive data and resources.
The average large-scale enterprise operation has different information tiers that are only accessible to specific employee cadres. Ensure unauthorized individuals, including employees, never get access to cloud system operations reserved for higher-level personnel.
Robust authentication mechanisms such as multi-factor authentication (MFA) can significantly reduce the risk of unauthorized access. For example, you may require users to pass two or more security protocols (e.g., password, fingerprint, or one-time token) when they log into the database from a new device.
In addition to robust authentication mechanisms like multi-factor authentication, another crucial element in ensuring comprehensive cloud system security is implementing physical access control. This involves using physical devices, such as key fobs or access cards, to regulate entry to specific areas or operations within the cloud system, further strengthening protection against unauthorized access. Through fob access control, you can control who has access to what.
This approach ensures users can only access the resources necessary for their specific roles, limiting the potential damage of account compromise.

Train Employees on Potential Cyber Threats and Safety Measures
Human error remains a common factor contributing to cyber breaches.
According to a 2023 Statista survey, 69% of Chief Information Security Officers (CISOs) in the United States agree that human error was their organization's most significant cyber vulnerability.
Employees who are careless with information and company assets in their custody may expose the company. As such, educating employees on methods cybercriminals use to execute their plans is crucial.
For example, social engineering is a popular trick cybercriminals use to breach enterprise cloud systems. This is a situation whereby the individual with ill intent socially manipulates an employee to give them access to the company's system, usually by pretending to be someone they're not.
Cybercriminals may also use other methods like phishing websites and malware attacks to execute malicious schemes.
Primarily, security begins with each employee with access to the cloud system. As such, you must educate employees on their role in protecting vital cloud systems. Proper employee training and awareness programs can help foster a security-conscious culture within an organization. To enhance the security of your cloud systems, consider using a robust password generator to create strong and unique login credentials.
Implement Encryption and Data Protection
Cybercriminals usually attack cloud systems to access company data and high-value information. This intent makes data encryption a crucial protective measure to discourage attempts on your cloud systems and digital assets.
Encrypting data at rest and in transit is a safeguard against data breaches and unauthorized access. As standard practice, your cloud service provider should offer encryption features to enable your organization to protect sensitive information effectively.
But, if built-in data protection features don't provide sufficient security, you should implement more robust encryption algorithms. In the rare event that hackers breach your cloud defenses, it's harder for cybercriminals to extract data of any note.
Furthermore, you must also consider data residency laws and compliance requirements. The United States has strict regulations regarding data privacy, storage, and protection. As such, you must ensure adherence to these laws to avoid penalties and preserve customer trust.
Establish Measures for Disaster Recovery and Backups
No security system is entirely invulnerable to cyber threats. For instance, it's impossible to guarantee 100% protection against social engineering or phishing attempts. Protection against such attacks falls to each employee's discretion.
As such, it's wise to implement a robust disaster recovery plan and backup for sensitive digital assets. Regularly backing up critical data in a secure location ensures your organization can quickly restore its system and maintain business continuity even during a successful breach.
In addition, it helps to automate disaster response measures. Manual measures often take time to implement. You may engage automation using Playbooks and Runbooks to respond to breaches and compromises on your systems quickly.

Create Off-Boarding Process To Prevent Exploitation From Departing Employees
Employees leave organizations for various reasons. Some leave on bad terms, bearing grudges against the company.
Disgruntled employees may desire payback and may use company resources in their possession to perpetrate their nefarious plans. In other situations, well-meaning individuals may get careless with sensitive information if they're no longer responsible for its security.
However, a comprehensive off-boarding process for departing employees can help your enterprise sidestep such cybersecurity loopholes. Ensure ex-employees leaving your company can no longer access your cloud systems, storage, data, or other intellectual property.
Implement Security Measures to Protect Cloud Systems from Cyber Attacks
Implementing the above measures guarantees increased safety of your enterprise cloud systems. You'll make it nearly impossible for cyber criminals to breach your systems.
And even if they manage to do that, data encryption measures will prevent them from accessing classified information.


 Copyright 2000-2026, WebSitePulse. All rights reserved.
Copyright 2000-2026, WebSitePulse. All rights reserved.